In the modern digital economy, data is the new currency, and the infrastructure that powers businesses is the new frontier for conflict. This reality has given rise to the colossal and indispensable B2B Cybersecurity industry, a sector dedicated to protecting organizations from a relentless barrage of digital threats. This market is not about selling antivirus software to consumers; it is a complex ecosystem of hardware, software, and services designed to safeguard the entire enterprise, from its cloud infrastructure and network perimeters to individual employee laptops and mobile devices. The core mission is to uphold the foundational principles of information security: confidentiality, ensuring data is accessible only to authorized users; integrity, maintaining the accuracy and trustworthiness of data; and availability, guaranteeing that systems and data are accessible when needed. As businesses undergo rapid digital transformation, embracing cloud computing, remote work, and IoT, their attack surface expands exponentially. Consequently, B2B cybersecurity has evolved from a niche IT function into a paramount, board-level strategic concern, essential for business continuity, regulatory compliance, and maintaining customer trust in an increasingly hostile digital world. This is the new cost of doing business.
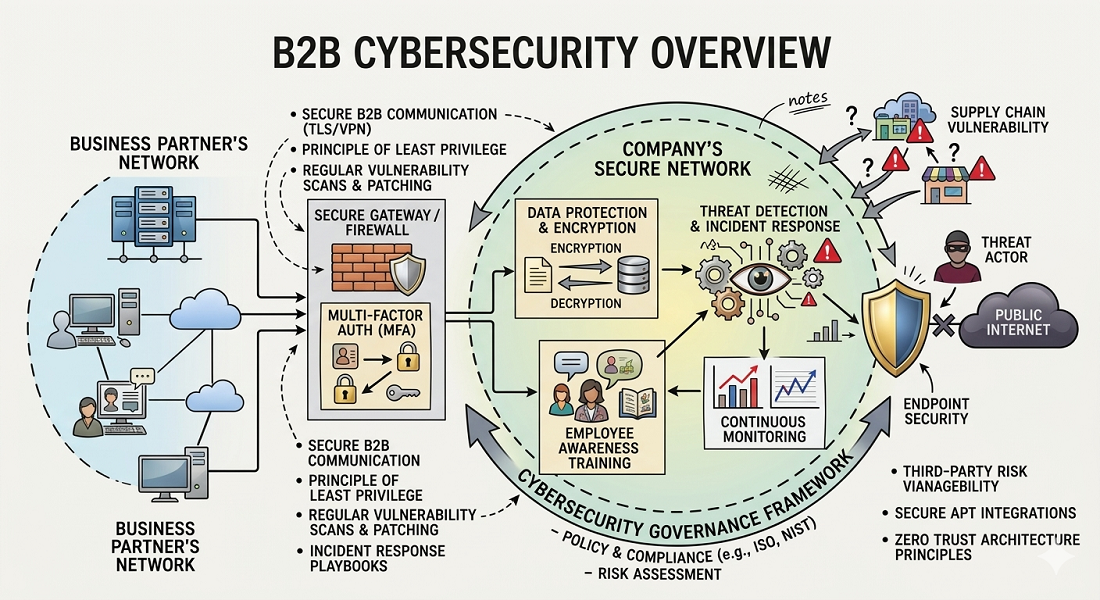
The B2B cybersecurity industry is structured around a multi-layered defense-in-depth strategy, acknowledging that no single product can provide complete protection. This approach involves deploying a suite of specialized solutions across various domains. Network Security forms the outer and internal perimeters, utilizing next-generation firewalls (NGFWs), intrusion detection and prevention systems (IDS/IPS), and secure web gateways to monitor and control traffic, preventing malicious actors from gaining a foothold. Endpoint Security focuses on protecting the devices where users do their work—laptops, servers, and mobile phones—using endpoint detection and response (EDR) platforms that have evolved far beyond traditional antivirus. Cloud Security has become a critical domain of its own, with tools like Cloud Security Posture Management (CSPM) and Cloud Workload Protection Platforms (CWPP) designed to secure complex cloud environments. Application Security (AppSec) focuses on finding and fixing vulnerabilities in the software an organization builds or buys, while Identity and Access Management (IAM) ensures that only the right people have access to the right resources. Together, these pillars form a comprehensive security posture, designed to prevent, detect, and respond to threats across the entire IT landscape, creating a resilient digital environment.
The threat landscape that this industry confronts is dynamic, sophisticated, and constantly evolving. The adversaries are not just lone hackers but well-organized criminal syndicates, state-sponsored Advanced Persistent Threat (APT) groups, and malicious insiders. Ransomware has evolved into a multi-billion dollar illicit industry, with attackers not only encrypting data but also exfiltrating it and threatening to leak it publicly, a tactic known as double extortion. Phishing and social engineering attacks have become remarkably sophisticated, using psychological manipulation to trick employees into revealing credentials or deploying malware. Supply chain attacks, where attackers compromise a trusted software vendor to distribute malware to all of their customers, have shown how interconnectedness can be exploited to devastating effect. These threats result in staggering financial losses, crippling operational downtime, severe reputational damage, and significant regulatory fines. The constant cat-and-mouse game between attackers and defenders is the primary engine of innovation in the B2B cybersecurity industry, forcing vendors to continuously develop more intelligent and automated defense mechanisms to keep pace with the adversary’s ever-changing tactics, techniques, and procedures. This is a perpetual arms race with no end in sight.
To combat these threats, the B2B cybersecurity industry relies on a combination of technology, processes, and people. Beyond the vast array of security products, organizations depend on well-defined processes and adherence to established frameworks like the NIST Cybersecurity Framework or ISO 27001 to structure their security programs. However, technology and processes are ineffective without skilled professionals. The industry is powered by a diverse workforce of security analysts, threat hunters, penetration testers, and compliance officers who operate on the front lines. The immense and persistent global cybersecurity skills gap has created a huge opportunity for the services segment of the market. Many businesses, particularly small and medium-sized enterprises (SMEs), lack the resources and in-house expertise to manage a robust security program. This has led to the explosive growth of Managed Security Service Providers (MSSPs). These firms act as an outsourced security operations center (SOC), providing 24/7 monitoring, threat detection, and incident response services, allowing businesses to leverage enterprise-grade security capabilities for a fraction of the cost of building them internally. This partnership model has become a cornerstone of the B2B cybersecurity industry today.
Explore Our Latest Trending Reports!